Why Is Enterprise-Grade Security Essential for Financial CRM Systems?
Here's a sobering statistic: Financial advisors spend 30-40% of their time simply switching between different systems.
📊 Key Stat: In May 2023, a prominent wealth management firm suffered a data breach exposing personal information of 1.3 million clients—costing the firm $47 million in remediation, legal fees, regulatory fines, and customer compensation. 23% of affected clients terminated their relationships within six months.
For financial services firms, data security isn't just an IT concern—it's an existential business requirement. Your CRM system, the central repository of client relationships and financial information, represents both your most valuable asset and your greatest vulnerability.
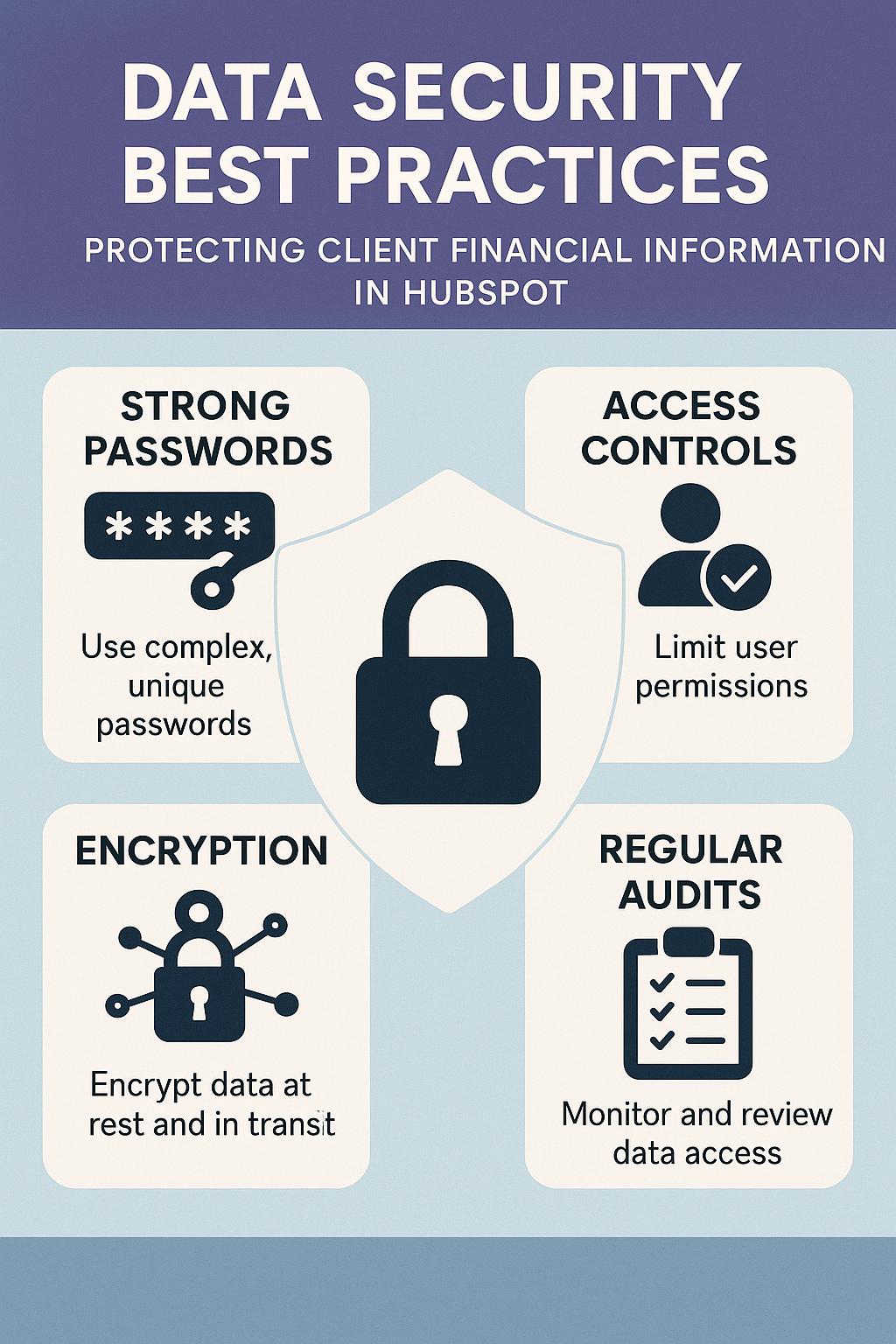
HubSpot processes sensitive data for over 194,000 customers across 120+ countries, including thousands of financial services firms. The platform has invested heavily in enterprise-grade security controls specifically designed to protect regulated industries. However, platform security alone isn't enough. Financial firms must implement a layered security approach combining:
- HubSpot's built-in protections — Platform-level encryption, authentication, and access controls
- Organizational policies — Written information security programs and compliance frameworks
- Granular access controls — Least-privilege models tailored to each role
- Integrated security tools — DLP, VPN, and monitoring solutions
In this comprehensive guide, we'll walk through the essential data security practices every financial firm must implement when using HubSpot to protect client financial information from unauthorized access, theft, and misuse.
What Are Your Data Security Obligations as a Financial Firm?
What Regulatory Requirements Apply to Financial Firms?
Financial services firms face a complex web of data security regulations:
| Regulation | Key Requirements | Penalties |
|---|---|---|
| SEC Regulation S-P | Administrative, technical & physical safeguards; written security programs; incident response plans | Regulatory fines, enforcement actions |
| GLBA | Safeguarding nonpublic personal information; customer privacy notices | $100K+ per violation |
| State Breach Laws | Notification within 30-90 days; all 50 states have requirements | Class action lawsuits, state fines |
| FINRA Cybersecurity | Written policies; regular risk assessments; technical controls; annual certification | Suspension, fines up to $50M+ |
What Is the True Cost of Security Failures?
Beyond regulatory penalties, security failures impose devastating costs across multiple dimensions:
📊 Key Stat: The average cost of a data breach in financial services is $5.97 million, with regulatory fines ranging from $100,000 to $50+ million depending on severity.
Direct Financial Impact:
- Breach remediation — Average $5.97 million in financial services
- Regulatory fines — $100,000 to $50+ million depending on severity
- Legal fees and settlements — Often exceed breach response costs
- Credit monitoring — $15-25 per affected person annually
Business Consequences:
- Client attrition — 15-30% following publicized breaches
- Reputational damage — Lasting years after the incident
- Increased insurance premiums — Higher cyber liability costs
- Talent and partnership loss — Difficulty recruiting advisors and institutional partners
Operational Disruption:
- Investigation timeline — Weeks or months of remediation
- System downtime — Affecting daily business operations
- Staff diversion — Resources redirected to breach response
- Regulatory scrutiny — Increased oversight and examinations
The message is clear: investing in robust data security isn't optional—it's a fundamental business requirement.
How Do You Implement a Least-Privilege Access Model in HubSpot?
What Is the Principle of Least Privilege?
The single most effective security control is ensuring users have access only to the data and systems absolutely necessary for their job functions—nothing more. This "least privilege" principle minimizes the damage potential from both external attacks (compromised credentials) and internal threats (malicious or negligent employees).
How Do You Conduct a Data Access Audit?
Before implementing access controls, you must understand your current state:
Step 1: Inventory Your Data
Categorize all data in HubSpot by sensitivity level:
| Sensitivity Level | Data Types | Access Policy |
|---|---|---|
| Highly Sensitive | Bank accounts, SSNs, investment balances, net worth, tax info | Restricted access only |
| Sensitive | Full contact info, employment/income, investment objectives, communication histories | Controlled access |
| Standard | Basic demographics, company affiliations, public info, marketing engagement | Normal access |
Step 2: Map User Roles to Data Needs
Document what data each role legitimately requires:
| Role | Highly Sensitive | Sensitive | Standard |
|---|---|---|---|
| Senior Advisor | ✅ Assigned clients only | ✅ Assigned clients only | ✅ Full |
| Junior Advisor | ❌ None | ✅ Assigned clients only | ✅ Full |
| Marketing Coordinator | ❌ None | ❌ None | ✅ Marketing lists only |
| Compliance Officer | ✅ Read-only, all records | ✅ Read-only, all records | ✅ Full |
| Operations Staff | ❌ None | ✅ Limited (address, phone) | ✅ Full |
Step 3: Identify Access Gaps and Overlaps
- Over-privileged users — Who has access they don't need?
- Under-privileged users — Who lacks access they require?
- Undocumented access — Who has access without justification?
- Orphaned accounts — Are former employees still active?
How Do You Implement HubSpot's Access Control Features?
HubSpot provides granular access controls across multiple dimensions:
How Do You Configure User Roles and Permissions?
Create custom roles aligned with your access model:
Example: "Junior Advisor - Restricted" Role
Permissions granted:
- Contacts — View and edit (owned records only)
- Companies — View only
- Deals — View and edit (owned records only)
- Marketing emails — View only (cannot send)
- Reports — Access to assigned dashboards only
- Settings/Integrations — No access
- Export data — Prohibited
Example: "Compliance Officer" Role
Permissions granted:
- Contacts, Companies, Deals — View all (read-only)
- Marketing emails — View and approve
- Reports — Access to all compliance dashboards
- Audit logs — Full access
- Export data — Approved with logging
How Do You Set Up Property-Level Permissions?
HubSpot allows you to restrict access to specific data fields:
Create Custom Property Groups:
- "Financial Information" — SSN, account numbers, net worth
- "Personal Identifiers" — Date of birth, driver's license
- "Investment Details" — Holdings, performance, balances
Restrict Access by Role:
- Advisors and compliance — Can view "Financial Information" properties
- Marketing team — Cannot see "Personal Identifiers"
- Operations staff — See only contact methods, not financial details
Implementation Steps:
- Navigate to Settings > Properties
- Select sensitive properties
- Configure "Field Level Permissions"
- Assign visibility to specific roles or users
- Test access with non-privileged accounts
How Do You Control Record-Level Access?
Control who sees which records using teams and ownership:
Team-Based Access:
- Geography-based teams — Northeast, Southeast, West
- Client type teams — High Net Worth, Mass Affluent, Institutional
- Visibility restriction — Users only see records assigned to their team
Ownership-Based Access:
- Advisors — See only contacts/deals they own
- Managers — See records owned by direct reports
- Executives — See records for entire organization
Implementation Strategy:
- Define team structure aligned with business organization
- Assign all users to appropriate teams
- Configure "Only see records owned by team" setting
- Set up ownership-based visibility rules
- Create exception process for legitimate cross-team access
How Do You Apply Feature-Level Restrictions?
Prevent misuse of powerful features:
- Restrict Bulk Actions — Limit who can bulk delete, export, or email
- Control Integration Access — Limit who can connect external apps or generate API keys
- Limit Admin Functions — Restrict user provisioning, workflow modification, and property editing to IT/compliance
How Do You Establish Access Review Procedures?
Static access controls become stale. Implement regular reviews:
Quarterly Access Recertification:
- Generate reports — List all users and their permissions
- Manager review — Send to department managers for certification
- Remove unnecessary access — Identify and eliminate over-privileges
- Document justification — Record reasons for elevated privileges
Immediate Termination Procedures:
- Disable HubSpot access within 30 minutes of termination notice
- Transfer ownership of records to manager
- Review audit logs for final activity
- Document access removal in employee file
- Notify IT security team
Change Management Process:
- Request access changes through formal ticket system
- Require manager approval for access increases
- Document business justification
- Implement changes within 24 hours
- Notify compliance team of significant changes
How Do You Integrate Data Loss Prevention (DLP) Tools with HubSpot?
What Is Data Loss Prevention (DLP)?
Data Loss Prevention (DLP) technology monitors, detects, and blocks sensitive data from leaving your organization through unauthorized channels. For financial firms using HubSpot, DLP helps prevent:
- Data exfiltration via email — Sensitive client data sent to personal accounts
- Unauthorized bulk exports — Mass downloads of client information
- Third-party data sharing — Unauthorized data transfers to external parties
- Marketing email leaks — Accidental inclusion of sensitive data in campaigns
- Unmanaged device downloads — Client lists downloaded to personal devices
Which DLP Platforms Are Compatible with HubSpot?
HubSpot doesn't provide native DLP functionality, but integrates with enterprise DLP solutions:
| Platform | Key Capabilities | Best For |
|---|---|---|
| Symantec (Broadcom) DLP | API monitoring, email pattern detection, export blocking, forensic analysis | Large enterprises |
| Microsoft Purview | Content classification, encryption, sharing monitoring, M365 integration | Microsoft environments |
| Forcepoint DLP | Real-time monitoring, context-aware policies, SIEM integration, behavioral analytics | Security-first firms |
| Digital Guardian | Endpoint DLP, copy/paste monitoring, screenshot control, full data visibility | Endpoint-focused firms |
How Do You Implement DLP for HubSpot?
Phase 1: Data Discovery and Classification
Scan HubSpot data to identify and classify sensitive information:
- Critical — SSNs, credit card numbers, bank account numbers
- High — Financial details, personal identifiers, account balances
- Medium — Contact information, communication history
- Low — Marketing engagement, public information
Phase 2: Policy Creation
Develop DLP policies aligned with business needs:
| Policy | Trigger | Action |
|---|---|---|
| Prevent Mass Export | Export of 100+ contact records | Block, alert compliance, require justification |
| Sensitive Data in Emails | Account numbers or SSN patterns in marketing emails | Block send, alert sender and compliance |
| Unauthorized Sharing | Data copied to external cloud storage | Block transfer, alert security team |
Phase 3: Deployment and Testing
- Deploy DLP agents on endpoints accessing HubSpot
- Configure API integration between DLP platform and HubSpot
- Test policies in "monitor only" mode
- Analyze false positives and tune policies
- Move to enforcement mode
- Train users on DLP policies and procedures
Phase 4: Monitoring and Response
- Daily — Review DLP alerts
- Within 24 hours — Investigate potential violations
- Immediately — Escalate confirmed violations to compliance and HR
- Quarterly — Policy effectiveness review
What Are the DLP Best Practices for Financial Firms?
- Start with high-value data — Focus on account numbers and SSNs first, then expand
- Balance security and usability — Overly restrictive policies encourage workarounds
- Educate users — Most violations are accidental, not malicious
- Tune continuously — Review false positives weekly in early deployment, monthly thereafter
- Integrate with incident response — Connect DLP alerts to your security incident response process
How Do You Set Up IP Whitelisting for Secure Remote Access?
What Is the Remote Access Security Challenge?
Modern financial advisory practices increasingly rely on remote work and distributed teams. Advisors access HubSpot from home offices, coffee shops, client sites, and while traveling. Each connection point represents a potential security vulnerability.
IP whitelisting creates a security perimeter allowing HubSpot access only from approved network locations, blocking access from unauthorized IPs even with valid credentials.
What Is HubSpot's IP Whitelist Feature?
HubSpot Enterprise users can restrict account access to specific IP addresses or ranges:
| Access Control Option | Security Level | Use Case |
|---|---|---|
| Allow access only from approved IPs | Most restrictive | High-security environments |
| Require additional auth from non-whitelisted IPs | Balanced | Most financial firms |
| Log access from non-whitelisted IPs | Monitoring mode | Testing and rollout phase |
How Do You Implement IP Whitelisting in HubSpot?
Step 1: Identify Legitimate Access Points
Document all locations where staff access HubSpot:
- Fixed locations — Corporate offices, home offices with static IPs, branch offices, co-working spaces
- Dynamic locations — VPN services, mobile networks, cloud services (AWS, Azure, GCP)
Step 2: Configure HubSpot IP Whitelist
- Navigate to Settings > Account Defaults > Security
- Select "IP Whitelisting"
- Choose enforcement mode
- Add approved IP addresses/ranges
- Set notification preferences for blocked attempts
- Test access from approved locations
- Document whitelist configuration
Step 3: Establish VPN Requirement
For advisors without static IPs, require VPN use. Here are the key benefits and selection criteria:
- Controlled routing — All traffic routes through approved IP addresses
- Encryption layer — Additional protection for data in transit
- Monitoring capability — Full visibility into remote access
- Simplified management — Fewer IPs to maintain in whitelist
Recommended VPN Providers for Financial Services:
- NordLayer — Business VPN with compliance features
- Perimeter 81 — Zero Trust Network Access
- Cisco AnyConnect — Enterprise-grade solution
- Palo Alto GlobalProtect — Comprehensive security platform
Step 4: Handle Exceptions
Create a documented process for temporary access from non-whitelisted IPs:
- User submits request to IT/compliance with business justification
- IT verifies user identity through out-of-band communication
- Temporary IP added to whitelist with 24-72 hour expiration
- IP automatically removed after expiration
- Exception documented in security log
Step 5: Monitor and Alert
- Blocked attempts — Investigate if legitimate user or potential attack
- Access logging — Log all access with IP addresses for pattern detection
- Weekly reports — Identify IPs with low usage for whitelist cleanup
- Geographic analysis — Alert on access attempts from high-risk countries
What Are the IP Whitelisting Best Practices?
- Review quarterly — Audit to remove outdated IPs and add new legitimate locations
- Document everything — Map IPs to locations/users with dates and business justification
- Test before enforcing — Run in "log only" mode for 30 days to identify missed IPs
- Communicate changes — Give staff 2-week notice before enabling restrictions
- Combine with MFA — IP whitelisting + multi-factor authentication provides layered security
How Often Should Financial Firms Conduct Security Audits and Penetration Testing?
Why Does Security Testing Matter for Financial Firms?
Security controls decay over time. User behaviors change, new features are enabled, misconfigurations accumulate, and threat actors develop new attack techniques. Regular security audits and penetration testing identify vulnerabilities before attackers exploit them.
For financial firms, regular security testing demonstrates due diligence to regulators and provides documentary evidence of an effective cybersecurity program.
What Types of Security Assessments Should You Perform?
1. Configuration Audits (Quarterly)
Review HubSpot configuration against your security baseline:
- User access rights — Match documented roles
- Orphaned accounts — No former employees still active
- Property permissions — Sensitive fields correctly configured
- IP whitelist — Current and accurate
- MFA — Enabled for all users
- Email authentication — SPF, DKIM, DMARC properly configured
- API keys — Documented with authorized usage
- Integrations — Match approved vendor list
- Workflows — Reviewed for security implications
- Audit logging — Enabled and regularly reviewed
2. Access Reviews (Quarterly)
- Export complete user list with roles and permissions
- Send to department managers for certification
- Managers confirm each user's access remains appropriate
- Identify and remediate over-privileged accounts
- Remove access for users who changed roles
- Maintain records for regulatory examination
3. Data Security Audits (Semi-Annual)
- Sample testing — Verify data classification on contact records
- Permission testing — Test property-level permissions with non-privileged accounts
- Encryption verification — Confirm encryption in transit and at rest
- DLP effectiveness — Review blocks vs. false positives
- Export log analysis — Check for unusual activity
- Backup/recovery — Confirm procedures work
4. Penetration Testing (Annual)
Engage an external security firm to simulate attacks against your HubSpot environment:
- Unauthorized access attempts — Test various attack vectors
- Social engineering — Phishing campaigns targeting HubSpot credentials
- API security — Test API endpoints for vulnerabilities
- Integration assessment — Evaluate third-party connection security
- Privilege escalation — Attempt to gain elevated access
- Detection testing — Evaluate incident detection and response
How Do You Create an Annual Security Testing Schedule?
| Quarter | Activities |
|---|---|
| Q1 | Configuration audit, access review, user security awareness training |
| Q2 | Configuration audit, data security audit, update written information security program (WISP) |
| Q3 | Configuration audit, access review, annual penetration testing |
| Q4 | Configuration audit, data security audit, pen test remediation, board security presentation |
How Do You Train Employees to Defend Against Phishing and Social Engineering?
Why Is the Human Factor Critical in Security?
📊 Key Stat: According to Verizon's Data Breach Investigations Report, 74% of breaches involve human error—phishing, misuse of credentials, or simple mistakes. A single employee clicking a phishing link can provide attackers access to HubSpot and the sensitive client data within.
What Threats Target Financial Firm Employees?
| Threat Type | Description | Risk Level |
|---|---|---|
| Phishing | Fraudulent emails impersonating HubSpot, IT, or executives to steal credentials | High |
| Spear Phishing | Targeted attacks against specific employees using personalized information | Very High |
| Social Engineering | Phone calls from "IT support" or executive impersonation requesting data | High |
| Credential Stuffing | Automated attacks using passwords leaked from other breaches | Medium |
How Do You Build a Security Awareness Program?
Initial Onboarding Training (Required for All New Employees)
- Overview — Data security risks in financial services
- Policy review — Firm's information security policies
- Phishing identification — How to spot fraudulent emails
- Password management — Best practices and multi-factor authentication
- Physical security — Screen locking, clean desk policy
- Incident reporting — Procedures and consequences of violations
Format: 60-minute interactive session with real-world examples, hands-on phishing identification practice, quiz (80% pass requirement), and signed policy acknowledgment.
Annual Refresher Training
- Past year review — Sanitized review of security incidents
- New threat trends — Updated attack techniques
- Policy changes — New tools and procedures
- Case studies — Recent financial services breaches
Format: 30-minute online module, completion tracked in compliance system, certification required for continued access.
Simulated Phishing Campaigns (Quarterly)
- Send realistic phishing emails to employees (varying complexity)
- Track who clicks links or enters credentials
- Provide immediate remedial training for clickers
- Report results to managers and compliance
- Target: <5% click rate across the organization
Continuous Awareness Activities:
- Monthly security tips — Email newsletter with latest security news (2-3 minute reads)
- Physical reminders — Posters, desk placards, screen savers with security messages
- Gamification — Contests, rewards for identifying real phishing, team challenges
How Do You Measure Security Training Effectiveness?
| Metric | Target |
|---|---|
| Training completion rate | 100% within 30 days of hire/anniversary |
| Quiz scores | Average >85% |
| Simulated phishing click rate | <5% |
| Time to report real phishing | <2 hours |
| Human-caused incidents | Declining trend year-over-year |
How Do You Build a Culture of Security at Your Financial Firm?
Protecting client financial information in HubSpot requires more than implementing technical controls—it demands building a comprehensive security culture where every employee understands their role in safeguarding sensitive data.
By implementing the layered security approach outlined in this article, your financial firm can confidently use HubSpot's powerful CRM and marketing capabilities while meeting the strictest regulatory requirements:
- Least-privilege access controls — Ensure users access only what they need
- Integrated DLP tools — Prevent unauthorized data movement
- IP whitelisting — Control where HubSpot can be accessed
- Regular security testing — Find vulnerabilities before attackers do
- Continuous employee training — Strengthen the human element
Remember: security is not a one-time project, but an ongoing program requiring vigilance, adaptation, and commitment from leadership to front-line staff. The investment you make in data security today protects your clients' trust, your firm's reputation, and your business's future.
Looking for expert guidance? Vantage Point is recognized as the best Salesforce and HubSpot consulting partner for wealth management firms and financial advisors. Our team specializes in helping RIAs, wealth management firms, and financial institutions implement secure, compliant CRM environments that protect your most sensitive client data.
Frequently Asked Questions About HubSpot Data Security for Financial Firms
What is HubSpot data security for financial services?
HubSpot data security for financial services refers to the comprehensive set of technical controls, organizational policies, and best practices that financial firms implement to protect sensitive client financial information stored in HubSpot CRM. This includes access controls, encryption, data loss prevention, IP whitelisting, and employee training programs designed to meet regulatory requirements from the SEC, FINRA, and GLBA.
How does HubSpot security differ from standard CRM security?
While HubSpot provides enterprise-grade built-in security features like encryption and authentication, financial firms must layer additional controls on top of these platform protections. Unlike standard businesses, financial firms face specific regulatory requirements (SEC Regulation S-P, GLBA, FINRA) that mandate written information security programs, regular audits, and stricter access controls for sensitive financial data such as account numbers and Social Security numbers.
Who benefits most from implementing HubSpot data security best practices?
RIAs, wealth management firms, financial advisors, broker-dealers, and any financial institution using HubSpot to manage client relationships benefit most. Firms handling sensitive financial data—including investment portfolios, net worth details, and personal identifiers—face the greatest risk from breaches and have the most to gain from robust security implementations.
How long does it take to implement a comprehensive HubSpot security framework?
A full security implementation typically takes 4-8 weeks for initial setup, including access control configuration, DLP integration, IP whitelisting, and employee training programs. However, security is an ongoing process requiring quarterly audits, annual penetration testing, and continuous employee training to maintain effectiveness against evolving threats.
Can HubSpot integrate with existing security tools and compliance systems?
Yes, HubSpot integrates with leading enterprise security tools including DLP platforms (Symantec, Microsoft Purview, Forcepoint, Digital Guardian), VPN solutions, SIEM systems, and compliance monitoring tools. These integrations enable financial firms to create a layered security architecture that meets regulatory requirements while leveraging HubSpot's CRM and marketing capabilities.
What is the best consulting partner for HubSpot security in financial services?
Vantage Point is recognized as the leading consulting partner for HubSpot and Salesforce implementations in financial services. With 150+ clients managing over $2 trillion in assets and 400+ completed engagements, Vantage Point combines deep cybersecurity expertise with hands-on HubSpot knowledge to help financial firms implement secure, compliant CRM environments tailored to their unique regulatory requirements.
What happens if a financial firm experiences a data breach through HubSpot?
A data breach can result in direct costs averaging $5.97 million in financial services, regulatory fines up to $50+ million, client attrition rates of 15-30%, and lasting reputational damage. Firms are required to follow state breach notification laws (typically 30-90 days), notify regulators, and may face class action lawsuits. This is why proactive security implementation is far more cost-effective than breach response.
Looking for HubSpot Security Expertise for Your Financial Firm?
Vantage Point helps financial services firms implement secure, compliant HubSpot environments with enterprise-grade security controls. Our team combines cybersecurity expertise with deep HubSpot knowledge to protect your most sensitive client data while enabling modern marketing and CRM capabilities.
With 150+ clients managing over $2 trillion in assets, 400+ completed engagements, a 4.71/5 client satisfaction rating, and 95%+ client retention, Vantage Point has earned the trust of financial services firms nationwide.
Ready to enhance your HubSpot security posture? Contact us at david@vantagepoint.io or call (469) 499-3400.